Crypto wallets represent a fundamental element of the blockchain ecosystem, being the entry point by which individuals maintain, handle, and transact with Internet-based assets. Regardless of whether you are a long-term Bitcoin investor, altcoin trader, NFT creator, or in decentralized finance (DeFi), the selection of crypto wallets has a direct impact on the security and usability of money, as well as control over it.
- What Are Crypto Wallets
- How Crypto Wallets Work
- Best Crypto Wallets: Top Picks and Comparison
- Detailed Review of the Best Crypto Wallets
- 1. Ledger Nano X
- 2. Trezor Model T
- 3. MetaMask
- 4. Trust Wallet
- 5. Exodus
- 6. Coinbase Wallet
- 7. Phantom
- Electrum
- How to Use These Wallet Reviews
- Secure Crypto Wallets for Maximum Asset Protection
- Wallets for Bitcoin and Altcoins
- Top Crypto Wallet Apps
- Digital Asset Wallets for Web3 and DeFi
- Custodial vs Non-Custodial Wallets: Which Is Right for You
- Custodial Wallet Advantages
- Custodial Wallet Risks
- Non-Custodial Wallet Advantages
- Non-Custodial Wallet Challenges
- Security Features to Look for in a Wallet
- How to Choose the Right Wallet for Crypto
- Wallet choice depends on:
- Security Features
- Custodial vs. Non-Custodial
- Backup & Recovery
- Supported Chains
- Common Wallet Mistakes and How to Avoid Them
- The Future of Crypto Wallets
- Conclusion
Crypto wallets do not have any middlemen, and unlike in the traditional banking system, the responsibility of holding the assets lies with the user. This is why one of the most significant choices in any crypto journey is the one that relates to crypto wallets. This is a comprehensive, unbiased, and informative analysis of wallet technologies, security models, custody options, and real-world examples of these technologies, and it compares the best crypto wallets in the market today to suit individuals, developers, and institutions.
Main Topic: What are Crypto Wallets?
Detailed Wallet Comparison
| Wallet Name | Type | Supported Assets | Key Security Features | Platforms | Custodial vs Non-Custodial | Best Use Case |
| Ledger Nano X | Hardware | BTC, ETH, 5,000+ | Secure Element chip, PIN, offline signing | Mobile, Desktop | Non-custodial | Long-term cold storage |
| Trezor Model T | Hardware | BTC, ETH, major altcoins | Open-source firmware, passphrase | Desktop | Non-custodial | Transparency-focused users |
| MetaMask | Web/Software | ETH, ERC-20 tokens | Encrypted local storage, hardware integration | Browser, Mobile | Non-custodial | DeFi and Web3 |
| Trust Wallet | Mobile | BTC, ETH, BNB, altcoins | Secure enclave, biometric authentication | Mobile | Non-custodial | Mobile-first users |
| Exodus | Software | 250+ assets | Local encryption, no data collection | Desktop, Mobile | Non-custodial | Beginners |
| Coinbase Wallet | Mobile/Web | BTC, ETH, tokens | Encrypted keys, dApp browser | Mobile, Browser | Non-custodial | Exchange-to-DeFi users |
| Phantom | Software | Solana ecosystem | Auto-lock, hardware integration | Browser, Mobile | Non-custodial | Solana users |
| Electrum | Desktop | Bitcoin | SPV verification, multisig | Desktop | Non-custodial | Advanced Bitcoin users |
What Are Crypto Wallets
Crypto wallets are either a computer program or a physical device to store cryptographic keys to blockchain networks. This is unlike what many people believe, that cryptocurrencies are not stored in crypto wallets. Rather than that, they store a set of personal keys that attest to the ownership of digital assets stored on a blockchain registry.
Why Crypto Wallets Exist
The networks based on blockchains are permissionless. Either one can address and trade without authorization, but the cost is liability. Crypto wallets exist to:
- Create and manage cryptographic keys
- Sign transactions securely
- Show balances and the history of transactions.
- Work with decentralized applications.
In the absence of wallets, users would have to touch private keys manually, which is not only inconvenient but also unsafe.
Custodial vs Non-Custodial Wallets
One of the key variations between crypto wallets is custody:
- Custodial wallets are wallets that hold the personal keys of the users. The access is usually secured by means of login credentials.
- Non-custodial wallets provide the user with complete authority over recovery phrases and private keys.
Although custodial wallets are convenient, they have a counterparty risk. Sovereignty is the priority of non-custodial wallets, but good personal security discipline is mandatory.
How Crypto Wallets Work
The technical explanation of the crypto wallets will assist a wallet user in making informed security choices.
Private Keys and Public Addresses
Every wallet produces a private key, which chemically derives a public key and a wallet address. The spending is approved with the help of the private key, whereas the public address enables other people to send money. The assets are freely controlled by the possessor of the private key.
Seed Phrases and Deterministic Wallets
The vast majority of modern wallets are designed on the basis of hierarchical deterministic (HD) architecture, which implies that a single seed phrase can be used to create thousands of addresses on a variety of blockchains. This makes the process of backing up simpler, but makes it more significant to protect seed phrases.
Best practices include:
- Writing of seed phrases on paper or metal backups
- Always keeping them not on electronic record.
- Having numerous backups at different locations.
Hot Wallets vs Cold Storage
- Hot wallets are also internet-connected and focused on usability.
- Cold storage wallets are offline and are security-oriented.
Experienced users often combine both approaches, using small balances in hot wallets and large balances in cold storage.
Best Crypto Wallets: Top Picks and Comparison
When choosing between the most popular crypto wallets, it is necessary to compare the usability, supported assets, security structure, and compatibility with the ecosystem.
Wallet Evaluation Criteria
Entering into a wallet was evaluated based on:
- Private key ownership
- Hardware security and encryption.
- Asset and network support
- Open-source transparency
- Historical security record
- User trust and adoption
Detailed Review of the Best Crypto Wallets
A closer examination of each of the best crypto wallets in the comparison table will be provided below. All wallets have their purposes, and it is better to know their advantages and weaknesses to be able to select the best of them.
1. Ledger Nano X
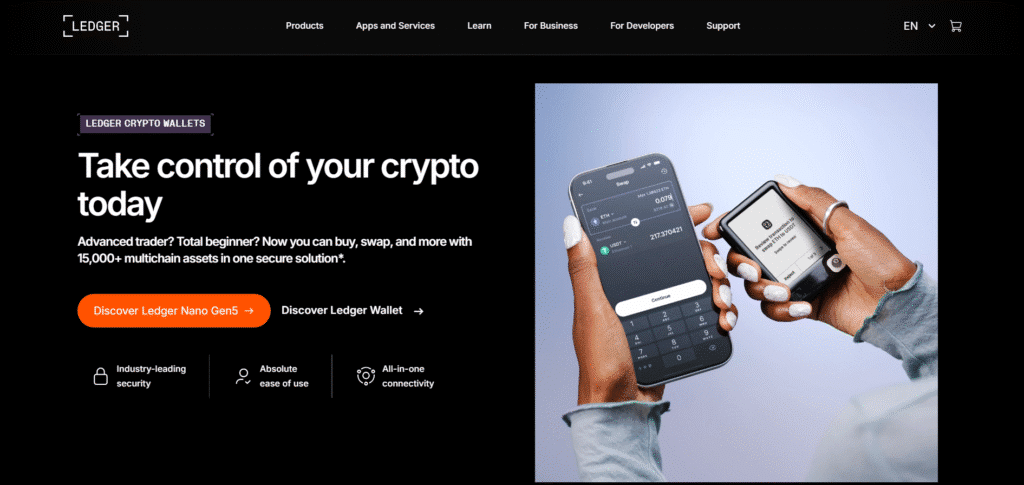
One of the most popular hardware wallets in the world is the Ledger Nano X, and it is oriented towards the user who values the long-term security of his or her assets. It stores private keys in a certified Secure Element chip where they do not actually leave the device, even when a computer or smartphone is connected.
The wallet allows putting money into thousands of types of cryptocurrencies and connects to the Ledger Live software, where customers can control their assets, stake supported currencies, and install blockchain programs. Bluetooth is supported in order to support mobile usage without key isolation.
Pros
- The presence of private keys is completely offline.
- Maintains a very high number of assets.
- Mobile and desktop support.
- Well-developed security architecture.
Cons
- Paid hardware device
- Lack of storage capacity in the installed applications.
- Needs to be updated on the firmware carefully.
Best for: Long-term investors and users who want to have as much security as possible in cold storage.
Check out the official site for complete details: https://www.ledger.com/
2. Trezor Model T
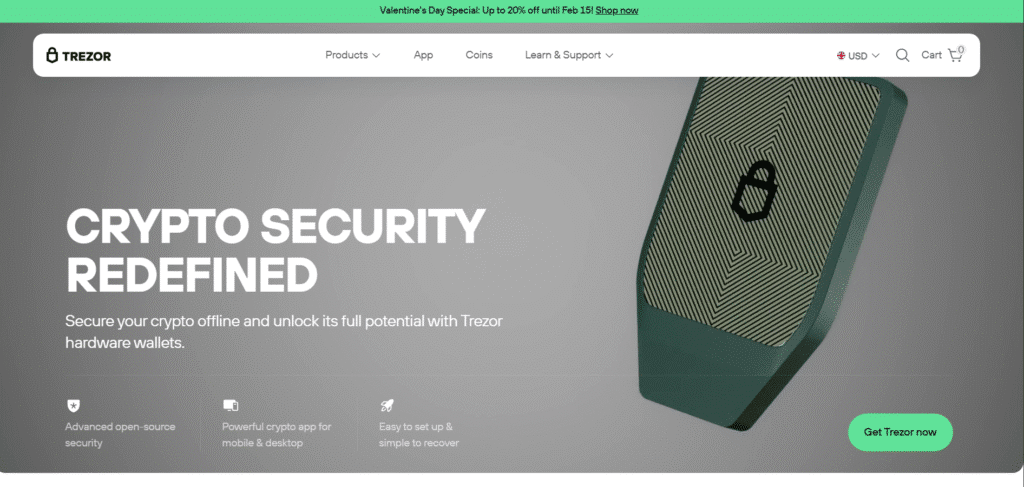
The Trezor Model T can be characterized by the open-source style and focus on transparency. Its firmware and software are also open to full auditing, unlike those of some of its competitors, and this is valuable to the security researcher or sophisticated user.
The device has a touchscreen interface, which is easier to operate when typing in PINs or passphrases. It accepts large-scale cryptocurrencies and links with several third-party wallet apps.
Pros
- Open-source software and firmware.
- Good reputation within the security fraternity.
- Touchscreen enhances usability.
- Advanced recovery options
Cons
- Higher price point
- Has smaller assets compared to Ledger.
- No secure element chip
Best for: Users who do not require maximum asset coverage but opt to have transparency and open-source security.
Check out the official site for complete details: https://trezor.io/
3. MetaMask
One of the most used software wallets in the Ethereum ecosystem is MetaMask. It can be used as a browser extension and a mobile app, and enables users to interact directly with decentralized applications.
MetaMask also stores its own keys locally on the device of the user and can use hardware wallets as an extra level of protection. It is highly embraced in DeFi, NFT marketplaces, and Web3 apps.
Pros
- Intensive integration with Ethereum and Web3.
- Easy dApp connectivity
- Hardware wallet compatibility
- Large user community
Cons
- Primarily Ethereum-focused
- Easy to abuse to fall prey to phishing.
- Browser-driven attack surface.
Best for: Participants interested in DeFi, NFT holders, and Web3 users.
Check out the official site for complete details: https://metamask.io/
4. Trust Wallet
Trust Wallet is a mobile-first, non-custodial wallet that has been made simple and supports a wide variety of assets. It is compatible with several blockchains and has an embedded dApp browser that allows one to access the decentralized applications straight through a smartphone.
The storage of the private keys is local and is encrypted on the machine, and the biometric authentication provides an added convenience.
Pros
- Basic and easy to use.
- Accepts numerous blockchains and tokens.
- Built-in dApp browser
- There was no registration of an account.
Cons
- Mobile (no desktop version)
- Weakly developed security controls.
- Reduction of the screen size amplifies the risk of errors.
Best for: Users who work more with mobile device-based asset management and beginners.
Check out the official site for complete details: https://trustwallet.com/
5. Exodus
Exodus pays much attention to user experience, providing an interface of high visual quality and easy installation. It also allows a very wide variety of digital assets and is built in with exchange functionality.
Although Exodus is not completely open source, it is non-custodial, and this might be a point of concern to very security-conscious users. Nonetheless, it is compatible with the hardware wallet in order to become more secure.
Pros
- Intuitive and smooth interface.
- Wide asset support
- Desktop and mobile versions
- Hardware wallet connectivity.
Cons
- Not fully open source
- In-built exchange fees can be high
- Limited advanced security customization.
Best for: New and intermediate users who want to use it easily across devices.
Check out the official site for complete details: https://www.exodus.com/
6. Coinbase Wallet
Coinbase Wallet is not a wallet of the Coinbase exchange but rather a self-custody wallet. It enables the users to have control over the private keys and, at the same time, enjoy a familiar interface.
The wallet accepts assets based on Ethereum, NFTs, and decentralized applications. Users who move their funds and use centralized exchanges to self-custody often use them.
Pros
- User-friendly interface
- Shift to the use of exchanges easily.
- Built-in dApp and NFT support
- Non-custodial design
Cons
- Less blockchain adoption than its competitors.
- The centralized brand can confuse the users.
- Less customizable to professionals.
Best for: Exchange users who are transitioning to self-custody and DeFi.
Check out the official site for complete details: https://www.coinbase.com/
7. Phantom
Phantom is a wallet that is developed on Solana. It offers rapid performance, implicit staking, and support of NFTs, which is a high-throughput design with Solana.
It has a wallet that is integrable with hardware wallets and both web and mobile versions.
Pros
- Optimized for Solana
- Quick and receptive interface.
- NFT and staking support
- Hardware wallet compatibility
Cons
- Limited to the Solana ecosystem
- Not applicable in multi-chain portfolios.
- Smaller ecosystem than Ethereum wallets.
Best for: Solana users who have major investments in the platform and applications.
Electrum
Electrum is an older and Bitcoin-only wallet that is popular with advanced users. It is more focused on performance, privacy, and customizability as opposed to visual design.
Electrum can be used with multisignature wallets, hardware wallets, and custom fee settings.
Pros
- Very secure Bitcoin realization.
- Advanced functionality.
- Lightweight and fast
- Multisig-Support
Cons
- Bitcoin-only
- Outdated interface
- Huge learning curve for novices.
Best for: Experienced Bitcoin users and those who want fine control.
How to Use These Wallet Reviews
This step-by-step analysis is a supplement to the comparison table, as it demonstrates the behavior of each wallet in practice, not only on paper. All these sections will assist the readers to recognize which among the best crypto wallets suits their security needs, technical comfort, and investment strategy.
Secure Crypto Wallets for Maximum Asset Protection
The most important aspect to consider in order to judge secure crypto wallets is security, and so, it is involved when handling large sums of capital.
Hardware Wallet Security
Hardware wallets store the private keys in inaccessible chips that cannot be exposed even in case the device that is connected to the wallet is tampered with. Physical verification should be done to ensure the transactions are not attacked remotely.
Multi-Signature Wallets
Multi-signature wallets have to be signed by more than one key before a transaction can take place. This is a typical configuration that is applied by institutions, DAOs, and family offices to avoid single-point failures.
Encryption and Secure Storage
Modern wallets encrypt local keys in a localized manner following advanced cryptographic specifications. But only the quality of the password used by the user and the security of the device can be as effective as encryption.
Wallets for Bitcoin and Altcoins
The selection of wallets for Bitcoin and altcoins should be based on compatibility with the blockchain.
Bitcoin-Focused Wallets
Bitcoin-only wallets are focused on network-specific optimizations like custom fee selection and full-node integration, and their emphasis is on security, privacy, and speed.
Multi-Chain Wallets
Multi-chain wallets are supported on Ethereum, Solana, Binance Smart Chain, and Polygon. They allow users to control diversified portfolios but make it more complicated.
The support of tokens as standard (ERC-20, BEP-20, SPL) defines the assets that can be stored and traded.
Top Crypto Wallet Apps
Mobile Wallets
The best crypto wallet applications are fast and convenient. They are good to be used on a daily basis, for small balances, and for on-the-run transactions.
Key features include:
- QR code scanning
- Biometric authentication
- Integrated dApp browsers
Desktop Wallets
Desktop wallets are more personalized and have more sophisticated controls, including:
- Custom transaction fees
- Node connectivity
- Multisig configurations
They only suit those users who have good operational security practices.
Digital Asset Wallets for Web3 and DeFi
DAWs have become identity layers in the decentralized ecosystems.
Web3 Integration
The wallets have become a form of login to:
- NFT marketplaces
- Decentralized exchanges
- DAO governance platforms
Browser wallets allow smooth communication with smart contracts but keep the user in custody.
WalletConnect and Interoperability
With the introduction of protocols such as WalletConnect, users can integrate mobile wallets with web applications without sacrificing security, making them easier to use.
Custodial vs Non-Custodial Wallets: Which Is Right for You
Custodial Wallet Advantages
- Password recovery options
- Customer support
- Simplified onboarding
Custodial Wallet Risks
- Platform insolvency
- Account freezes
- Regulatory intervention
Non-Custodial Wallet Advantages
- Full ownership
- Permissionless access
- Censorship resistance
Non-Custodial Wallet Challenges
- Losses are irreversible in case of mishandling of seed phrases.
- Increased accountability to the user.
Security Features to Look for in a Wallet
Wallet Security Checklist
| Feature | Description | Why It Matters |
| Seed phrase backup | Offline recovery mechanism | Prevents permanent asset loss |
| Multi-signature | Requires multiple approvals | Reduces theft risk |
| Hardware integration | Offline key storage | Protects from malware |
| Biometric authentication | Fingerprint or face ID | Prevents unauthorized access |
| Open-source code | Public audits | Enhances transparency |
How to Choose the Right Wallet for Crypto
Wallet choice depends on:
Security Features
Select wallets with a private key option, encryption, and recovery. Hot wallets are provided with digital protection in the form of phishing warnings and secure backups, whereas cold wallets have better protection in the form of offline storage.
Custodial vs. Non-Custodial
Custodial wallets take care of your keys, and non-custodial wallets leave it up to you. Self-custody wallets are the most preferred ones but need to be carefully backed up.
Backup & Recovery
Recovery keys and seed phrases are necessary. Cold wallets are backed with offline backups, whereas hot wallets tend to offer cloud or manual backup. Funds may be lost indefinitely without backups.
Supported Chains
A wallet should have a variety of blockchains and tokens. Hot wallets tend to be more compatible in nature, whereas cold wallets specialize in major assets. Supported networks should always be checked before they are selected.
Beginners might be more usability-oriented, whereas more advanced users are fine-grained and security-oriented.
Common Wallet Mistakes and How to Avoid Them
Frequent mistakes include:
- Taking screenshots of seed phrases
- Installing fake wallet apps
- Ignoring firmware updates
- Signing blind transactions
The greatest defenses are education and skepticism.
The Future of Crypto Wallets
The innovation of wallets is increasing, and the trends are:
- Programmable permission wallets that are smart.
- Social recovery in place of seed phrases.
- Wallets that combine staking, lending, and governance.
With the rise in the use of blockchains, wallets are going to be more of a complete financial operating system.
Conclusion
The crypto wallets are the engine of digital asset ownership, linking users to decentralized networks, with them having direct accountability of their own security. Modern crypto wallets can address the needs of users of different levels of experience with the help of hardware devices that can be used as cold storage or mobile applications that can help conduct daily transactions. To safeguard assets in a more complex ecosystem, it is important to understand the architecture of wallets, models of custody, and security. With the increase in the use of blockchains, wallets will proceed to develop into multitasking systems that will further bolster their position as an important infrastructure in the digital finance future.
Disclaimer: BFM Times acts as a source of information for knowledge purposes and does not claim to be a financial advisor. Kindly consult your financial advisor before investing.
What is the most secure crypto wallet in 2026?
The most secure crypto wallets in 2026 are hardware cold storage options like Ledger (Nano X / Stax) and Trezor Safe 3 that keep private keys offline and protect against hacks.
Which wallet is best for beginners in 2026?
The best wallet for beginners in 2026 is ZenGo (or similar MPC-based wallets) that combine simple user experience with strong security and no seed-phrase complexity.
Which wallet offers best all-around balance of security & usability in 2026?
Exodus Wallet is one of the best all-around crypto wallets in 2026 combining strong security, built-in exchange, multi-asset support and easy interface for most users.