Key Insights
- Smart contract coding errors can sometimes create vulnerabilities worth millions of dollars that hackers can exploit.
- Private key compromises through phishing and social engineering can drain millions from exchange hot wallets.
- Flash loan attacks also manipulate prices and break the logic in DeFi protocols.
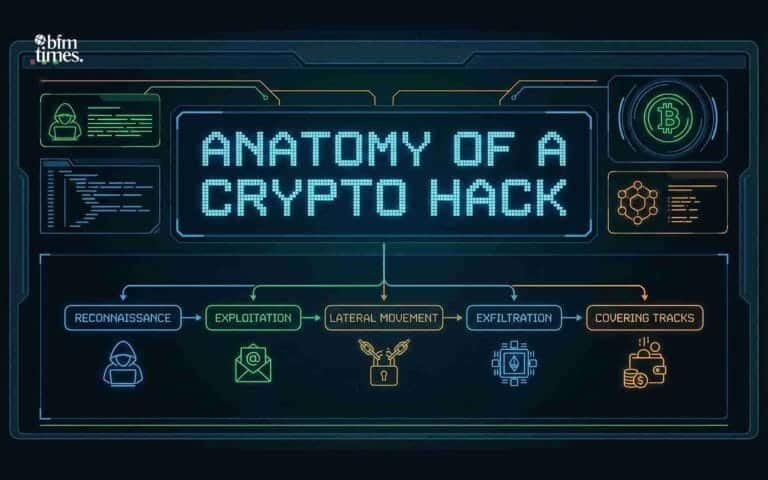
The crypto industry has grown into a multi-trillion-dollar market. Yet billions of dollars disappear every year through security breaches. Blockchain technology itself is secure, but the infrastructure built around it still faces constant attacks.
This said, understanding how crypto hacks happen can reveal some interesting patterns. Most breaches come from predictable flaws in code or human behaviour, and here is a look at some of the most popular.
Smart Contract Vulnerabilities
Smart contracts are the powerhouse of Defi. These self-executing programs automatically handle agreements and transfer digital assets when required.
The “code is law” principle makes them powerful, and this same principle is what makes bugs so damaging.
A single coding error can become a multi-million-dollar Security Breaches very quickly.
Reentrancy Attacks
Reentrancy is arguably one of the most notorious smart contract flaws. This attack lets a hacker write a contract that repeatedly calls a withdrawal function. This function in the hacker’s contract repeatedly requests withdrawals from the victim contract before it has a chance to update its balance.
To understand this better, think of withdrawing money from an ATM that doesn’t check your balance until after you leave.
This way, you can withdraw more and more money until the ATM becomes empty.
The DAO hack in 2016 was a perfect example of this vulnerability perfectly. An early DAO on Ethereum fell victim to a reentrancy flaw, where the attacker drained approximately $60 million worth of Ether.

The 2016 DAO hack was a perfect example of a reentrancy attack | source: X
This breach led to the controversial hard fork that split the chain into Ethereum and Ethereum Classic.
The attack worked because the vulnerable contract sent funds before updating its internal accounting. The attacker’s contract received funds and immediately called the withdrawal function again. This loop continued until the victim contract was empty.
Logic Flaws Target Complex Operations
Beyond simple coding mistakes, logic flaws can also affect how contracts handle complicated operations. Cross-chain bridges are particularly vulnerable to this kind of attack.
These protocols lock assets on one blockchain to issue wrapped tokens on another.
They then become massive targets because they hold enormous amounts of value.
The Ronin Bridge exploit in 2022 saw attackers compromise five of nine validator keys required to approve withdrawals. This simple majority let them drain over $600 million in ETH and USDC.

The Ronin Bridge hack saw more than $600 million stolen | source: X
The Poly Network exploit in 2021 was the same story, but a different attack vector. A cross-chain message error in the smart contract let attackers bypass ownership checks and steal over $600 million in various tokens.
Interestingly, the attacker later returned the funds and claimed to be pointing out Security Breaches issues.
Private Key Compromises
While Smart contract flaws attack decentralised code. Private key theft is the opposite, because it targets centralised control points. A private key is the ultimate cryptographic password proving fund ownership, and if a hacker gets control of this key, very bad things can happen.
Hot Wallet Breaches
Exchanges keep portions of assets in hot wallets connected to the internet. This makes sure that there is always liquidity for daily trading operations. However, weak Security Breaches around these wallets can lead to devastating losses.
The BitMart hack in 2021 was a prime example of this vulnerability. Hackers obtained a private key securing one of the exchange’s hot wallets and drained almost $200 million in various cryptocurrencies across two blockchain networks.

Hackers stole nearly $200 million from the BitMart hack | source: X
While hot wallets can be relatively easy to break into, cold storage (offline wallets) provides better Security Breaches . However, they can’t service immediate withdrawal requests.
This explains why centralised exchanges use both simultaneously.
Social Engineering
Human psychology is often easier to exploit than code. Social engineering manipulates people into revealing confidential information or granting access. These attacks bypass all technical Security Breaches completely.
The Ronin Bridge hack involved some degree of social engineering where a senior Sky Mavis employee (Ronin’s developer) received a spear-phishing attack via email. These highly personalised emails are designed to lure targets into breaking their own Security Breaches .
At the end of the social engineering attack, the hacker was able to steal a validator node’s private key.
They then used an unrevoked allowlist permission for another key. This combination secured the 5-of-9 majority that was needed to drain the bridge and more than half a billion dollars went down the drain.
In this case, technical Security Breaches was solid but human vulnerability created the breach.
Economic Exploits
Modern crypto hacks are now targeting economic logic, rather than code bugs. Flash loans allow attackers to carry out particularly clever attacks, in which they borrow massive uncollateralized amounts.
This kind of attack works because the users have to repay within the same transaction block, and no actual capital is required upfront.
Hence, they borrow and borrow until the smart contract is drained.
Price Oracle Manipulation Drains Protocols
Attackers use flash loans to temporarily manipulate asset prices. They borrow huge amounts of one token and aggressively buy or sell another token on low-liquidity markets.
This artificially spikes or crashes prices.
The manipulated price feeds into the price oracles that DeFi protocols use and the attacker then takes out massively under-collateralised loans from victim protocols.
They repay the flash loan and keep the profit, with the entire hack happening in seconds within a single transaction.
Governance Exploits
The Beanstalk Farms hack in 2022 showed how attackers combine multiple exploit types. The hacker used a flash loan to get enormous amounts of governance tokens (and therefore instant voting power)
The attacker proceeded to approve a malicious governance proposal that transferred all protocol funds (over $180 million).
Disclaimer: BFM Times acts as a source of information for knowledge purposes and does not claim to be a financial advisor. Kindly consult your financial advisor before investing.